This is an application that automates the issuance and renewal of Let's Encrypt certificates for the Azure App Service. We have started to solve the following issues
- Support for multiple App Services
- Easy to deploy and configure
- Highly reliable implementation
- Ease of Monitoring (Application Insights, Webhook)
You can manage multiple App Service certificates in a single application.
If you need to use the certificate for a variety of services, consider using the Key Vault version of Acmebot v3.
https://github.com/shibayan/keyvault-acmebot
The Key Vault version can be used with services that support Key Vault certificates such as App Service / Application Gateway / CDN / Front Door.
- Azure Web Apps and Azure Functions (Windows)
- Azure Web Apps (Linux) / Web App for Containers (Windows and Linux, requires Azure DNS)
- Azure App Service Environment (Windows and Linux)
- Issuing a certificate to the deproyslot
- Issuing Certificates for Zone Apex Domains
- Issuing certificates with SANs (subject alternative names) (one certificate for multiple domains)
- Wildcard certificate (requires Azure DNS)
- Support for multiple App Services in a single application
- Azure Subscription
- App Service with a registered custom domain
- Email address (required to register with Let's Encrypt)


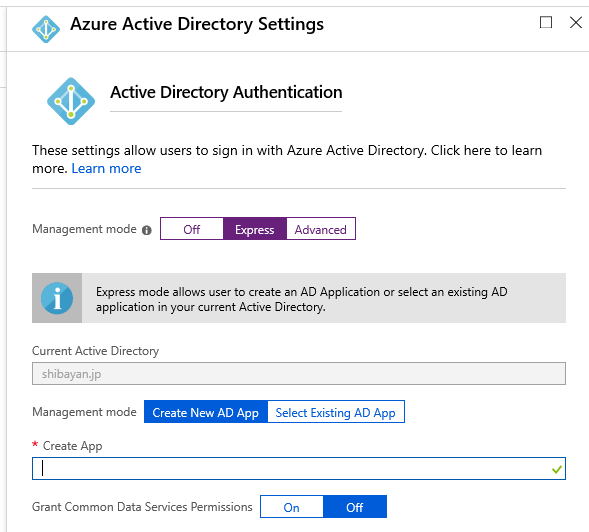
Open the Authentication / Authorization menu in Azure Portal and enable App Service authentication. Select the Login with Azure Active Directory as the action to perform if the request is not authenticated. We recommend using Azure Active Directory as your authentication provider, but it works with other providers as well, although it's not supported.
Select Azure Active Directory as the authentication provider, select Express as the management mode, and select OK.
Finally, you can save your previous settings to enable App Service authentication.
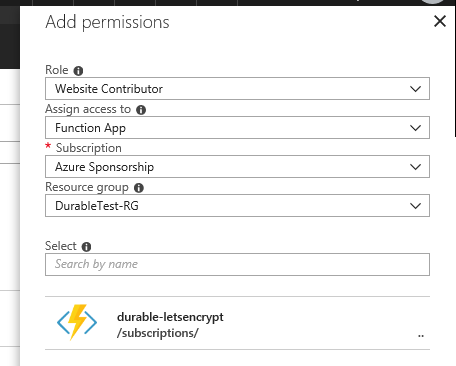
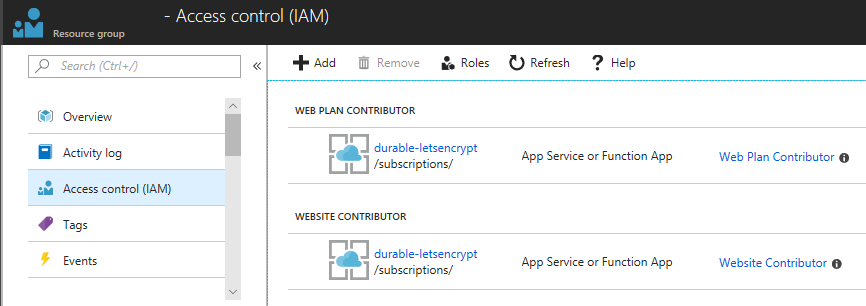
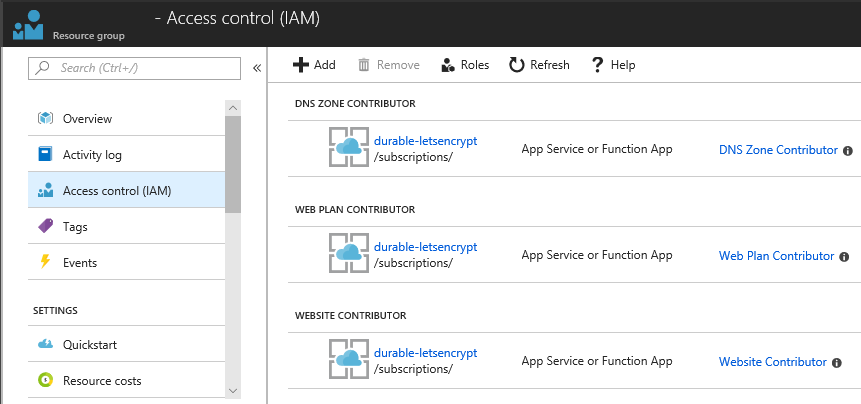
Open the Access control (IAM) of the target resource group and assign the roles Website Contributor and Web Plan Contributor to the deployed application.
Remarks
If the App Service Plan associated with the App Service exists in a separate resource group, you should assign a Website Contributor to the resource group where the App Service exists, and a Web Plan Contributor to the resource group where the App Service Plan exists.
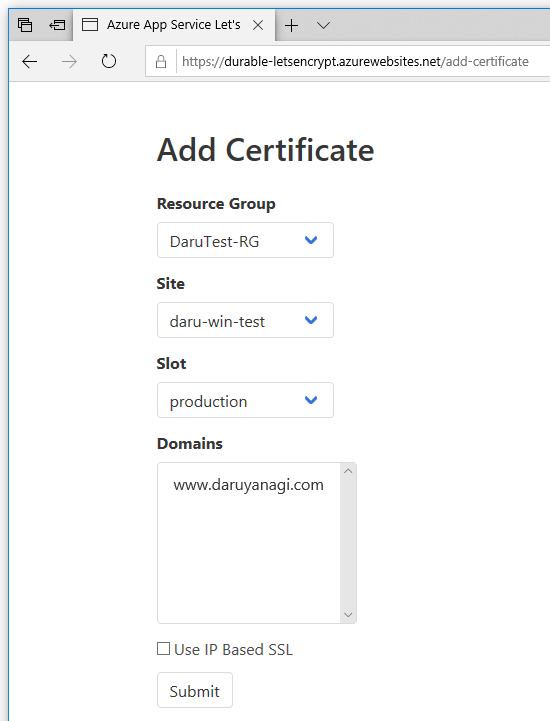
Access https://YOUR-FUNCTIONS.azurewebsites.net/add-certificate with a browser and authenticate with Azure Active Directory and the Web UI will be displayed. Select the target App Service and domain from that screen and run it, and after a few tens of seconds, the certificate will be issued.
If the Access control (IAM) setting is not correct, nothing will be shown in the drop-down list.
Because Azure DNS is required to issue wildcard certificates or certificates for Linux, assign the role of DNS Zone Contributor in the resource group containing the target DNS zone.
To issue certificates for "App Service on Linux" and "Web App for Container", Azure DNS is always required.
Once every few days, the application performs an expiration check on the certificate of the issuer of Let's Encrypt Authority X3 or Let's Encrypt Authority X4.
The default check timing is 00:00 UTC. If you need to change the time zone, use WEBSITE_TIME_ZONE to set the time zone.
The application is automatically updated so that you are always up to date with the latest version. If you explicitly need to deploy the latest version, restart the Azure Function.
Causes Azure REST API error at GetSite or Dns01Precondition error occurs
The role assignment to the target resource group may be incorrect or not yet reflected, and it may take up to 30 minutes for the IAM settings to take effect.
CheckDnsChallenge failed: _acme-challenge.{domain}.com value is not correct error occurs
In order for the certificate to be created, the bot needs to create a TXT DNS record for _acme-challenge in Azure DNS. This error occurs when the TXT record isn't being served. One cause of this may be that the nameservers for your domain may be pointing to the domain registrar, rather than Azure DNS. Make sure that you have properly delegated the domain to Azure DNS: Host your domain in Azure DNS
CheckHttpChallenge failed: http://{domain}/.well-known/acme-challenge/{challenge} is InternalServerError status code error occurs
It seems like URL rewrite error, so please try inheritInChildApplications="false" settings for web.config under wwwroot.
https://www.hanselman.com/blog/ChangingASPNETWebconfigInheritanceWhenMixingVersionsOfChildApplications.aspx
- ACMESharp Core by @ebekker
- Durable Functions by @cgillum and contributors
- DnsClient.NET by @MichaCo
This project is licensed under the Apache License 2.0