- Keychain/Keystore Access for React Native
- Installation
- Usage
- API
setGenericPassword(username, password, [{ accessControl, accessible, accessGroup, service, securityLevel }])getGenericPassword([{ authenticationPrompt, service, accessControl }])resetGenericPassword([{ service }])getAllGenericPasswordServices()setInternetCredentials(server, username, password, [{ accessControl, accessible, accessGroup, securityLevel }])hasInternetCredentials(server)getInternetCredentials(server, [{ authenticationPrompt }])resetInternetCredentials(server)requestSharedWebCredentials()(iOS and visionOS only)setSharedWebCredentials(server, username, password)(iOS and visionOS only)canImplyAuthentication([{ authenticationType }])(iOS and visionOS only)getSupportedBiometryType()getSecurityLevel([{ accessControl }])(Android only)- Options
- Important Behavior
- Manual Installation
- Unit Testing with Jest
- Notes
- Maintainers
- For Developers / Contributors
- License
-
Run
yarn add react-native-keychain1 a. Only for React Native <= 0.59:
$ react-native link react-native-keychainand checkMainApplication.javato verify the package was added. See manual installation below if you have issues withreact-native link. -
Run
pod installinios/directory to install iOS dependencies. -
If you want to support FaceID, add a
NSFaceIDUsageDescriptionentry in yourInfo.plist. -
Re-build your Android and iOS projects.
import * as Keychain from 'react-native-keychain';
async () => {
const username = 'zuck';
const password = 'poniesRgr8';
// Store the credentials
await Keychain.setGenericPassword(username, password);
try {
// Retrieve the credentials
const credentials = await Keychain.getGenericPassword();
if (credentials) {
console.log(
'Credentials successfully loaded for user ' + credentials.username
);
} else {
console.log('No credentials stored');
}
} catch (error) {
console.log("Keychain couldn't be accessed!", error);
}
await Keychain.resetGenericPassword();
};See KeychainExample for fully working project example.
Both setGenericPassword and setInternetCredentials are limited to strings only, so if you need to store objects etc, please use JSON.stringify/JSON.parse when you store/access it.
setGenericPassword(username, password, [{ accessControl, accessible, accessGroup, service, securityLevel }])
Will store the username/password combination in the secure storage. Resolves to {service, storage} or rejects in case of an error. storage - is a name of used internal cipher for saving secret; service - name used for storing secret in internal storage (empty string resolved to valid default name).
Will retrieve the username/password combination from the secure storage. Resolves to { username, password, service, storage } if an entry exists or false if it doesn't. It will reject only if an unexpected error is encountered like lacking entitlements or permission.
Will remove the username/password combination from the secure storage. Resolves to true in case of success.
Will retrieve all known service names for which a generic password has been stored (e.g., setGenericPassword).
Note: on iOS this will actully read the encrypted entries, so it will trigger an authentication UI if you have encrypted any entries with password/biometry.
setInternetCredentials(server, username, password, [{ accessControl, accessible, accessGroup, securityLevel }])
Will store the server/username/password combination in the secure storage. Resolves to { username, password, service, storage };
Will check if the username/password combination for server is available in the secure storage. Resolves to true if an entry exists or false if it doesn't.
Will retrieve the server/username/password combination from the secure storage. Resolves to { username, password } if an entry exists or false if it doesn't. It will reject only if an unexpected error is encountered like lacking entitlements or permission.
Will remove the server/username/password combination from the secure storage.
Asks the user for a shared web credential. Requires additional setup both in the app and server side, see Apple documentation. Resolves to { server, username, password } if approved and false if denied and throws an error if not supported on platform or there's no shared credentials.
Sets a shared web credential. Resolves to true when successful.
Inquire if the type of local authentication policy is supported on this device with the device settings the user chose. Should be used in combination with accessControl option in the setter functions. Resolves to true if supported.
On iOS and visionOS: Get what type of hardware biometry support the device can use for biometric encryption. Resolves to a Keychain.BIOMETRY_TYPE value when supported and enrolled, otherwise null.
On Android: Get what type of Class 3 (strong) biometry support the device has. Resolves to a Keychain.BIOMETRY_TYPE value when supported, otherwise null. In most devices this will return FINGERPRINT (except for Pixel 4 or similar where fingerprint sensor is not present).
This method returns
null, if the device haven't enrolled into fingerprint/FaceId. Even though it has hardware for it.
Get security level that is supported on the current device with the current OS. Resolves to Keychain.SECURITY_LEVEL enum value.
| Key | Platform | Description | Default |
|---|---|---|---|
accessControl |
All | This dictates how a keychain item may be used, see possible values in Keychain.ACCESS_CONTROL. |
None |
accessible |
iOS, visionOS | This dictates when a keychain item is accessible, see possible values in Keychain.ACCESSIBLE. |
Keychain.ACCESSIBLE.WHEN_UNLOCKED |
accessGroup |
iOS, visionOS | In which App Group to share the keychain. Requires additional setup with entitlements. | None |
authenticationPrompt |
All | What to prompt the user when unlocking the keychain with biometry or device password. | See authenticationPrompt Properties |
authenticationType |
iOS, visionOS | Policies specifying which forms of authentication are acceptable. | Keychain.AUTHENTICATION_TYPE.DEVICE_PASSCODE_OR_BIOMETRICS |
service |
All | Reverse domain name qualifier for the service associated with password. | App bundle ID |
storage |
Android only | Force specific cipher storage usage during saving the password | Select best available storage |
rules |
Android only | Force following to a specific security rules | Keychain.RULES.AUTOMATIC_UPGRADE |
| Key | Platform | Description | Default |
|---|---|---|---|
title |
All | Title of the authentication prompt when requesting a stored secret. | Authenticate to retrieve secret |
subtitle |
Android only | Subtitle of the Android authentication prompt when requesting a stored secret. | None. Optional |
description |
Android only | Description of the Android authentication prompt when requesting a stored secret. | None. Optional |
cancel |
Android only | Negative button text of the Android authentication prompt when requesting a stored secret. | Cancel |
| Key | Description |
|---|---|
USER_PRESENCE |
Constraint to access an item with either Touch ID or passcode. |
BIOMETRY_ANY |
Constraint to access an item with Touch ID for any enrolled fingers. |
BIOMETRY_CURRENT_SET |
Constraint to access an item with Touch ID for currently enrolled fingers. |
DEVICE_PASSCODE |
Constraint to access an item with a passcode. |
APPLICATION_PASSWORD |
Constraint to use an application-provided password for data encryption key generation. |
BIOMETRY_ANY_OR_DEVICE_PASSCODE |
Constraint to access an item with Touch ID for any enrolled fingers or passcode. |
BIOMETRY_CURRENT_SET_OR_DEVICE_PASSCODE |
Constraint to access an item with Touch ID for currently enrolled fingers or passcode. |
Note #1:
BIOMETRY_ANY,BIOMETRY_CURRENT_SET,BIOMETRY_ANY_OR_DEVICE_PASSCODE,BIOMETRY_CURRENT_SET_OR_DEVICE_PASSCODE- recognized by Android as a requirement for Biometric enabled storage (Till we got a better implementation);Note #2: For Android we support only two states:
None(default) andFingerprint(use only biometric protected storage);Facerecognition fails with "User not authenticated" exception, see issue #318
Refs:
| Key | Description |
|---|---|
WHEN_UNLOCKED |
The data in the keychain item can be accessed only while the device is unlocked by the user. |
AFTER_FIRST_UNLOCK |
The data in the keychain item cannot be accessed after a restart until the device has been unlocked once by the user. |
ALWAYS |
The data in the keychain item can always be accessed regardless of whether the device is locked. |
WHEN_PASSCODE_SET_THIS_DEVICE_ONLY |
The data in the keychain can only be accessed when the device is unlocked. Only available if a passcode is set on the device. Items with this attribute never migrate to a new device. |
WHEN_UNLOCKED_THIS_DEVICE_ONLY |
The data in the keychain item can be accessed only while the device is unlocked by the user. Items with this attribute do not migrate to a new device. |
AFTER_FIRST_UNLOCK_THIS_DEVICE_ONLY |
The data in the keychain item cannot be accessed after a restart until the device has been unlocked once by the user. Items with this attribute never migrate to a new device. |
Refs:
| Key | Description |
|---|---|
DEVICE_PASSCODE_OR_BIOMETRICS |
Device owner is going to be authenticated by biometry or device passcode. |
BIOMETRICS |
Device owner is going to be authenticated using a biometric method (Touch ID or Face ID). |
Refs:
| Key | Description |
|---|---|
TOUCH_ID |
Device supports authentication with Touch ID. (iOS only) |
FACE_ID |
Device supports authentication with Face ID. (iOS only) |
OPTIC_ID |
Device supports authentication with Optic ID. (visionOS only) |
FINGERPRINT |
Device supports authentication with Fingerprint. (Android only) |
FACE |
Device supports authentication with Face Recognition. (Android only) |
IRIS |
Device supports authentication with Iris Recognition. (Android only) |
Refs:
If set, securityLevel parameter specifies minimum security level that the encryption key storage should guarantee for storing credentials to succeed.
| Key | Description |
|---|---|
ANY |
no security guarantees needed (default value); Credentials can be stored in FB Secure Storage; |
SECURE_SOFTWARE |
requires for the key to be stored in the Android Keystore, separate from the encrypted data; |
SECURE_HARDWARE |
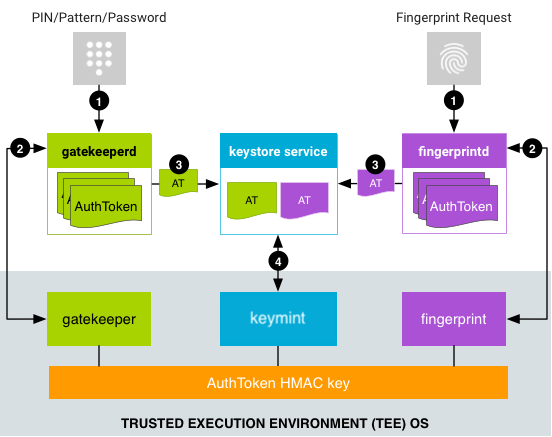
requires for the key to be stored on a secure hardware (Trusted Execution Environment or Secure Environment). Read this article for more information. |
| Key | Description |
|---|---|
FB |
Facebook compatibility cipher |
AES |
Encryptions without human interaction. |
RSA |
Encryption with biometrics. |
| Key | Description |
|---|---|
NONE |
No rules. Be dummy, developer control everything |
AUTOMATIC_UPGRADE |
Upgrade secret to the best available storage as soon as it is available and user request secret extraction. Upgrade not applied till we request the secret. This rule only applies to secrets stored with FacebookConseal. |
As a rule the library will try to apply the best possible encryption for storing secrets. Once the secret is stored however its does not try to upgrade it unless FacebookConseal was used and the option 'SECURITY_RULES' is set to 'AUTOMATIC_UPGRADE'
Q: What will happen if user disables/drops biometric usage?
A: User will lose ability to extract secret from storage. On re-enable biometric access to the secret will be possible again.
Q: Is it possible to implement automatic downgrading?
A: From security perspective any Automatic downgrading is treated as "a loss of the trust" point. Developer should implement own logic to allow downgrade and deal with "security loss". (My recommendation - never do that!)
Q: How to enable automatic upgrade for FacebookConseal?
A: Do call getGenericPassword({ ...otherProps, rules: "AUTOMATIC_UPGRADE" }) with extra property rules set to AUTOMATIC_UPGRADE string value.
Q: How to force a specific level of encryption during saving the secret?
A: Do call setGenericPassword({ ...otherProps, storage: "AES" }) with forced storage.
Note: attempt to force storage
RSAwhen biometrics is not available will force code to reject call with errors specific to device biometric configuration state.
- Right click on Libraries, select Add files to "…" and select
node_modules/react-native-keychain/RNKeychain.xcodeproj - Select your project and under Build Phases -> Link Binary With Libraries, press the + and select
libRNKeychain.a. - make sure
pod 'RNKeychain'is not in yourPodfile
Option: With CocoaPods
Add the following to your Podfile and run pod update:
pod 'RNKeychain', :path => '../node_modules/react-native-keychain'
For iOS 10 you'll need to enable the Keychain Sharing entitlement in the Capabilities section of your build target. (See screenshot). Otherwise you'll experience the error shown below.
Error: {
code = "-34018";
domain = NSOSStatusErrorDomain;
message = "The operation couldn\U2019t be completed. (OSStatus error -34018.)";
}
- Edit
android/settings.gradleto look like this (without the +):
rootProject.name = 'MyApp'
include ':app'
+ include ':react-native-keychain'
+ project(':react-native-keychain').projectDir = new File(rootProject.projectDir, '../node_modules/react-native-keychain/android')- Edit
android/app/build.gradle(note: app folder) to look like this:
apply plugin: 'com.android.application'
android {
...
}
dependencies {
implementation fileTree(dir: 'libs', include: ['*.jar'])
implementation 'com.android.support:appcompat-v7:23.0.1'
implementation 'com.facebook.react:react-native:0.19.+'
+ implementation project(':react-native-keychain')
}- Edit your
MainApplication.java(deep inandroid/app/src/main/java/...) to look like this (note two places to edit):
package com.myapp;
+ import com.oblador.keychain.KeychainPackage;
....
public class MainActivity extends extends ReactActivity {
@Override
protected List<ReactPackage> getPackages() {
return Arrays.<ReactPackage>asList(
new MainReactPackage(),
+ new KeychainPackage()
);
}
...
}On Android builds that use proguard (like release), you may see the following error:
RNKeychainManager: no keychain entry found for service:
JNI DETECTED ERROR IN APPLICATION: JNI FindClass called with pending exception java.lang.NoSuchFieldError: no "J" field "mCtxPtr" in class "Lcom/facebook/crypto/cipher/NativeGCMCipher;" or its superclasses
If so, add a proguard rule in proguard-rules.pro:
-keep class com.facebook.crypto.** {
*;
}
The keychain manager relies on interfacing with the native application itself. As such, it does not successfully compile and run in the context of a Jest test, where there is no underlying app to communicate with. To be able to call the JS functions exposed by this module in a unit test, you should mock them in one of the following two ways:
First, let's create a mock object for the module:
const keychainMock = {
SECURITY_LEVEL_ANY: "MOCK_SECURITY_LEVEL_ANY",
SECURITY_LEVEL_SECURE_SOFTWARE: "MOCK_SECURITY_LEVEL_SECURE_SOFTWARE",
SECURITY_LEVEL_SECURE_HARDWARE: "MOCK_SECURITY_LEVEL_SECURE_HARDWARE",
setGenericPassword: jest.fn().mockResolvedValue(),
getGenericPassword: jest.fn().mockResolvedValue(),
resetGenericPassword: jest.fn().mockResolvedValue(),
...
}-
Read the jest docs for initial setup
-
Create a
react-native-keychainfolder in the__mocks__directory and addindex.jsfile in it. It should contain the following code:
export default keychainMock;-
In your Jest config, add a reference to a setup file
-
Inside your setup file, set up mocking for this package:
jest.mock('react-native-keychain', () => keychainMock);Now your tests should run successfully, though note that writing and reading to the keychain will be effectively a no-op.
The module will automatically use the appropriate CipherStorage implementation based on API level:
- API level 16-22 will en/de crypt using Facebook Conceal
- API level 23+ will en/de crypt using Android Keystore
Encrypted data is stored in SharedPreferences.
The setInternetCredentials(server, username, password) call will be resolved as call to setGenericPassword(username, password, server). Use the server argument to distinguish between multiple entries.
Android implementation has behavioural specifics incurred by existing inconsistency between implementations by different vendors. E.g., some Samsung devices show very slow startup of crypto system. To alleviate this, a warm-up strategy is introduced in Android implementation of this library.
Using default constructor you get default behaviour, i.e. with the warming up on.
private List<ReactPackage> createPackageList() {
return Arrays.asList(
...
new KeychainPackage(), // warming up is ON
...
)Those who want finer control are required to use constructor with a builder which can be configured as they like:
private List<ReactPackage> createPackageList() {
return Arrays.asList(
...
new KeychainPackage(
new KeychainModuleBuilder()
.withoutWarmUp()), // warming up is OFF
...
)If you need Keychain Sharing in your iOS extension, make sure you use the same App Group and Keychain Sharing group names in your Main App and your Share Extension. To then share the keychain between the Main App and Share Extension, use the accessGroup and service option on setGenericPassword and getGenericPassword, like so: getGenericPassword({ accessGroup: 'group.appname', service: 'com.example.appname' })
Refs:
- https://developer.apple.com/documentation/localauthentication
- https://developer.apple.com/documentation/security
This package supports macOS Catalyst.
This package supports visionOS.
On API levels that do not support Android keystore, Facebook Conceal is used to en/decrypt stored data. The encrypted data is then stored in SharedPreferences. Since Conceal itself stores its encryption key in SharedPreferences, it follows that if the device is rooted (or if an attacker can somehow access the filesystem), the key can be obtained and the stored data can be decrypted. Therefore, on such a device, the conceal encryption is only an obscurity. On API level 23+ the key is stored in the Android Keystore, which makes the key non-exportable and therefore makes the entire process more secure. Follow best practices and do not store user credentials on a device. Instead use tokens or other forms of authentication and re-ask for user credentials before performing sensitive operations.

Joel Arvidsson Author |

Vojtech Novak Maintainer |

Pelle Stenild Coltau Maintainer |

Oleksandr Kucherenko Contributor |
MIT © Joel Arvidsson 2016-2020